Security Risk Assessment Consultants
What are the consequences of not conducting a security risk assessment during project planning?
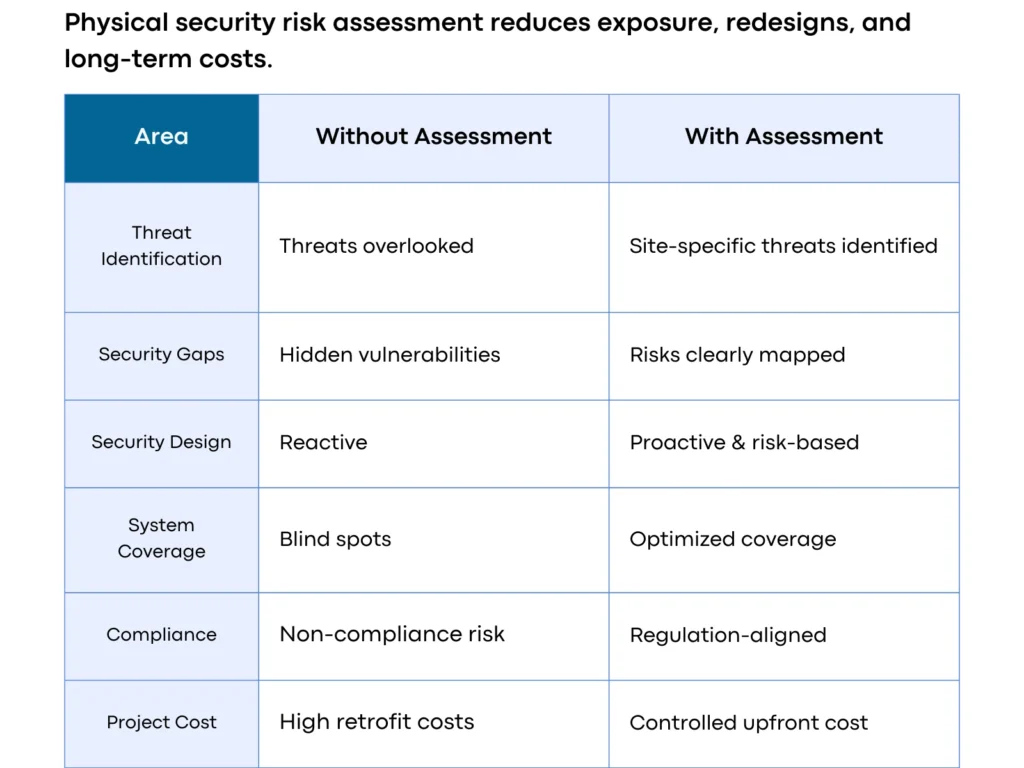
Projects require a formal security assessment to avoid the risk of security blind spots, non-compliance, and higher retrofit costs after construction. Skipping this step is harmful as it leads to additional costs in redesigns, safety suits, and legal liabilities post-occupancy. Security risk assessments will dominate physical security design.
SECURITY RISK ASSESSMENT CONSULTANTS, SAUDI ARABIA
Security risk assessment is a process of defining an organization’s potential threats and risks and fortifying its security structure. Our team uses a question-based approach to identify the specific scope of assessment, such as
- What is the scope of this security risk assessment?
- Is it meeting the organization’s objective?
- Does it consider the context of the organization, its needs, and requirements?
We customize our solution based on the security threat assessment conducted considering your organization’s unique context, objective, and resource limitations. In our conclusion report, we tailor an approach that empowers you with a roadmap for mitigating vulnerabilities and strengthening your complete physical security background in Saudi Arabia
Our Steps For Security threat & Risk Assessment
Assets at Risk Identification
Risk & Vulnerability Assessment
Security Gap Analysis
Risk/Vulnerabilities Resilience
Security Master Plan
Review Document & Assurance
Who We Work With






Our work
Our Most Successful Projects
Discover our diverse range of projects showcasing our expertise in ELV and security design solutions across the Middle East and Africa.
Contact us
Testimonials
What Our Clients think about Us?

Nithin Mane
Niyo MEP Consultants would like to thank DSP Consultants team for their professional ELV design support services for the hospitalitality projects. The quality of the design was outstanding and the scope of work was delivered on time. We will be happy to work with you again in the future.
Zaid Rababa
I am Impressed by DSP Consultants' expertise. Your active projects with major developers in UAE and KSA speak volumes.
Khalid A. Hamidadin
We, Hamdan Studio, express our sincere gratitude to the DSP Consultants team for their exceptional professionalism and unwavering commitment in delivering EL V Design services promptly and with utmost proficiency.
Mohideen Abdul Khader
National Engineering Bureau would like to thank DSP Consultants team for their professional work and commitment to deliver their ELV Design services on time and in professional way. We wish you all the best and looking forward to have long term professional relationship with you.
Sayed Abouelella
Appreciated all the efforts been contributed by your Team and especially by you Asif , and big gratitude for Eng. Fayaz who never leave us alone since the first step of the project till we got the approval, Thank you so much gentlemen and we shall continue the same support.
OTHER SERVICES KSA
Explore how we help you
Explore our array of top-notch design, consulting, and engineering solutions tailored for the Kingdom of Saudi Arabia.
FAQ
Frequently Asked Questions
Q1. What is a security risk and threat assessment?
Security Threat and Risk Assessment (STRA) is a process of evaluating the seucurity risks facing an organization and providing security consulting solutions to minimize the Threat and Risks.
Q2. What are the benefits of a security risk and threat assessment?
- Improved security posture
- Reduced risk of security incidents
- Increased compliance
- Improved decision-making
- Leading the business development
Q3. What are the different types of security risk and threat assessments?
- Internal security risk and threat assessment
- External security risk and threat assessment
- Physical security risk and threat assessment
- Information security risk and threat assessment
Q4. How much does it cost for a complete security risk assessment for project?
The cost of the risk assessment depends on various factors related to the project, including the type of application, its location, surrounding conditions, and local regulatory requirements. For a more accurate cost estimate, it is recommended to get in touch with a professional and experienced Security Risk and Threat Assessment Consultant in KSA.
COMPANY CERTIFICATIONS