1. What are the services provided by Security Consultants in Dubai?
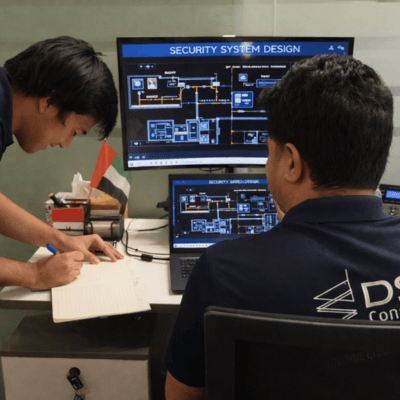
Security consultants are specialists who offer a wide array of services, such as physical security system design, security risk assessment, CCTV system design, access control planning, security master planning, and even blast mitigation design services. Their main aim is to ensure your project, facility, business, and its operations are protected against security risks with local compliance. Acoustic testing and study are important to ensure compliance with local regulations in Saudi Arabia, removing potential disturbances and supporting sustainable urban development.
2. How is security risk assessment conducted by security consultants?
Security risk assessment is a prominent step before designing physical security systems for any project or building. Security threat or risk assessment helps understand potential vulnerabilities that have to be mitigated or avoided at all costs. Security consultants then recommend tailored security measures, ensuring they meet physical, electronic, and operational security standards.
3. What is included in a security master plan?
A security master plan is a strategic roadmap that includes reports, designs, methodologies, and a strategy for the security design of a project. It typically includes threat analysis, vulnerability study, physical and electronic security measures, emergency procedures, and a compliance plan. Security consultants customize it based on the facility’s specific needs, following local and international security guidelines.
4. When do you need Blast Analysis Consultants?
Blast analysis is essential for high-profile projects where safety from explosive threats is critical; blast analysis consultants are needed to create security plans and design structures that can adhere to blast loads and are resilient to minimize damage and ensure compliance with safety standards.
What are the services provided by Security Consultants in Dubai?
Security consultants are specialists who offer a wide array of services such as physical security risk assessments, security master planning, security systems design, CCTV systems design, access control planning, and even blast mitigation design services. Their main aim is to ensure your project, facility, business, and its operations are protected against security risks with local compliance.