Counter-Drone Security Consultants
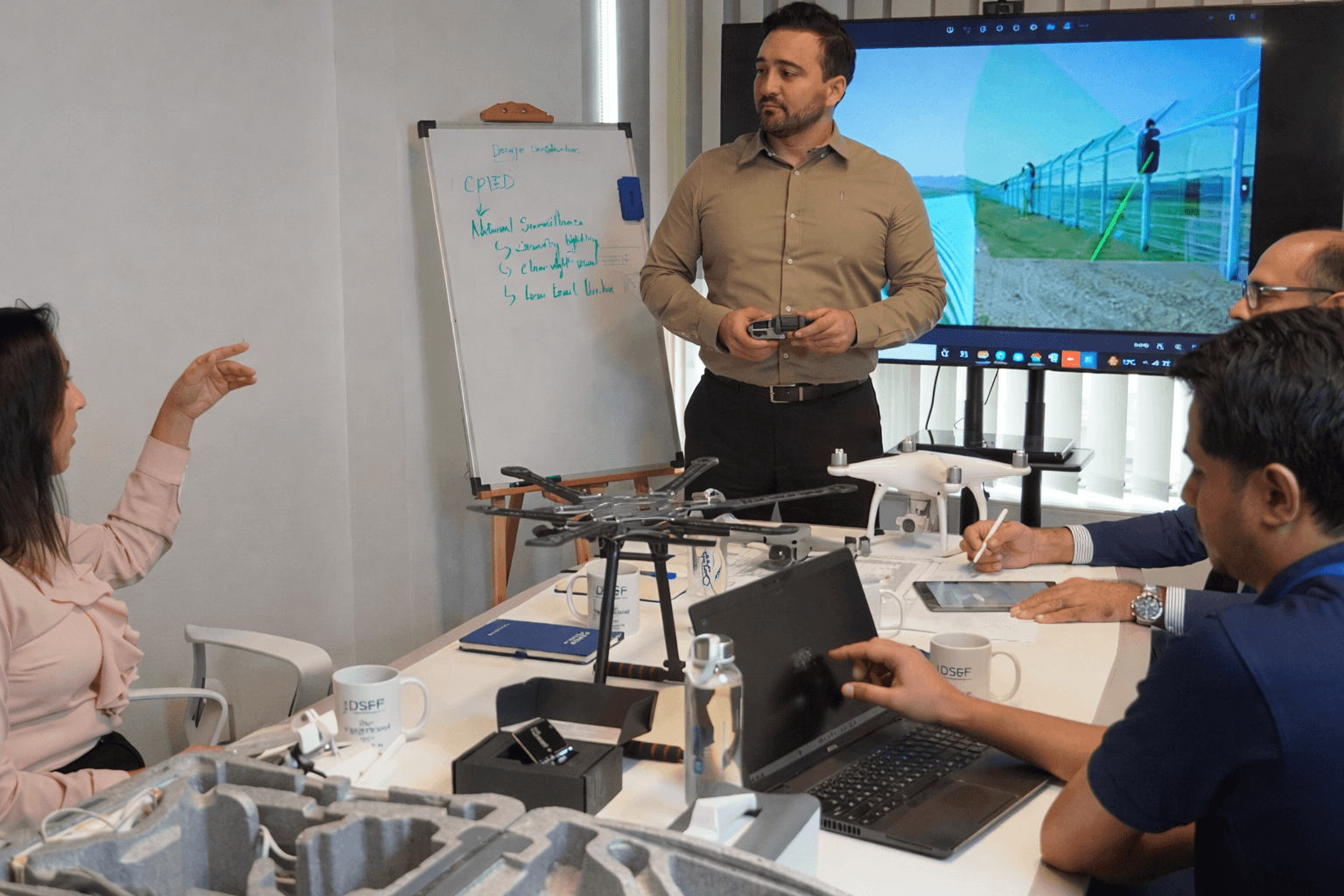
DSP Consultants delivers security by carefully considering the latest technological threats and vulnerabilities within modern systems.
Drones, while a powerful defense tool, can also turn into a weapon if misused, jeopardizing the security and privacy of vital resources in the region.
DSP Consultants’ leadership is an expert in creating anti-drone systems that help in detecting, identifying, tracking, and neutralizing unauthorized UAVs that could pose a security threat.
We specialize in security consultancy services, technical solutions, and comprehensive expertise in unmanned aerial vehicles, focusing on multilayer detection and mitigation of threats posed by unauthorized drones.
Specialize in deploying and assessing multiple counter-drone solutions, protecting drones from interference, and operating in stealth (hidden) mode.
Our developed studies help to implement counter-drone solutions tailored to the needs of both public and private sectors.
Multi-layered Detection and Mitigation
Flow Sequence for Drones Detection and Mitigation
1. Detection:
Tracking systems identify the presence of a drone using technologies such as radar (a system that uses radio waves to detect objects), RF sensors (which detect radio frequency signals), acoustic sensors (which pick up sound waves), or cameras.
2. Identification:
The identification system detects it, then it analyzes the signal or visual data to identify whether the drone is unauthorized or is a security threat.
3. Tracking:
The system tracks the drone’s location, flight path, speed, and occasionally the operator’s location in real time.
4. Neutralization/ Mitigation:
If the UAV is authorized and is considered a threat, the system can stop it using methods such as the following:
- RF Jamming
- GPS Spoofing
- Signal Takeover
- Physical Interception

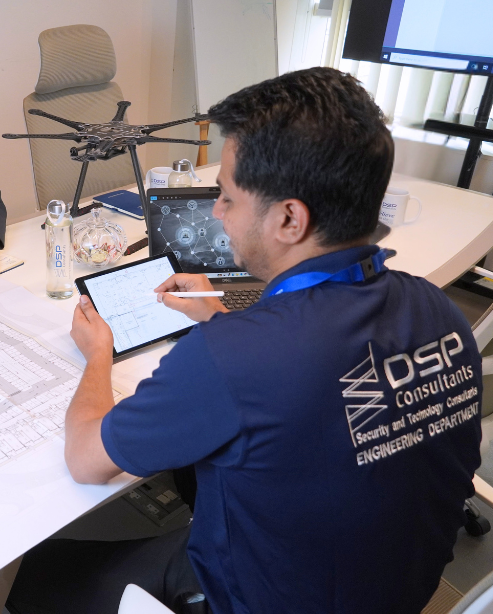
Security Insights and Expertise Driven Systems
DSP Consultants create counter-drone solutions with expertise in physical security threat mitigation and assessment to protect critical infrastructure, airports, government buildings, events, and military sites from threats such as unauthorized surveillance, sabotage, or attacks.
For companies like DSP Consultants working in physical security design, anti-drone strategies are increasingly integrated into perimeter security and risk assessments for sensitive developments.
We Work For Security Of Facilities:

Residential

Commercial Mixed-use
Government
High Rise
Contact us
COMPANY CERTIFICATIONS