Physical Security Designs Abu Dhabi
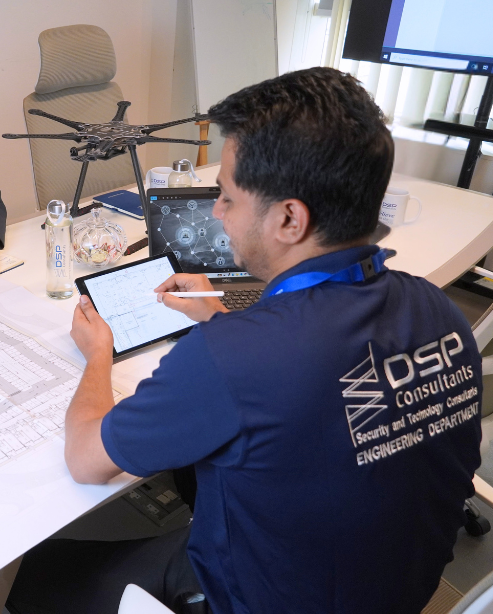
#1 Security Consultants in Abu Dhabi
DSP Consultants provide a full spectrum of Physical Security Consulting services in Abu Dhabi by assessing and designing physical protection systems through the complete integration of physical security components.
Security Systems Designs by our specialist team are based on three pillars
- Electronic Security
- Architectural Security
- Operational Security

We at DSP Consultants realize the requirement of effective integration of physical security components using relevant technologies. Our security design deliverables cover,
- Concept and plan design
- Schematic Drawings
- Detailed Design
- System specifications
- Tender documentation
- Commissioning verification
- Supervision by specialist engineers
- Reporting of site services, and specific action, when necessary, after inspection & auditing.
Our Approach to Physical Security Consultation
- We pay special attention to every aspect of the ‘what, where, when, and how of your premises/ properties considering custom-based studies.
- We conduct comprehensive & efficient Security Audits and surveys to provide a complete security assessment & analysis and make relevant recommendations & studies.
- We then develop a security plan aligned with your objectives and work with you to achieve them safely and as smoothly as po

Customized Security Strategies for Your Business Partnering with You to Achieve Optimal Security
SECURITY RISK ASSESSMENT CONSULTANTS, DUBAI
DSP Consultants offers Risk Assessment and Vulnerability studies according to the ISO-31000 and ASIS instructions for each category of the facility.

Blast analysis is to identify the potential consequence of a blast on the infrastructure based on the threat assessment, building evaluation, and blast modeling results, security professionals assess the overall risk and likelihood of an attack, the potential for casualties and property damage, and the building's ability to withstand an explosion developing a threat mitigation strategy.

Conducting security risk analysis to identify and evaluate a comprehensive risk management strategy.

Security operational procedures and practices (SecOps procedures) are vital components of a security risk assessment. Identifying Gaps and weaknesses, developing mitigation strategies, and evaluating effectiveness, are a few examples of security operational practices.

Security risk assessment is the first step but a security gap analysis is the most prominent step which compares an organization’s desired security posture to their current security position. The gap analysis compares existing security controls such as access controls, firealarms, etc against industry best practices, security standards, or internal security policies. This reveals areas where controls are missing, inadequate, or not functioning properly as required.

It is a detailed action plan for implementing security measures based on identified risks by doing a security risk and threat assessment. It specifies security measures that help organizations effectively strengthen their security posture.

A well-defined and tested business continuity plan demonstrates an organization's capability to handle disruptions. This can reduce the overall security risk, as attackers are less likely to succeed if they know the organization can recover quickly.

Testimonials
What Our Clients think about Us?

Nithin Mane
Niyo MEP Consultants would like to thank DSP Consultants team for their professional ELV design support services for the hospitalitality projects. The quality of the design was outstanding and the scope of work was delivered on time. We will be happy to work with you again in the future.
Zaid Rababa
I am Impressed by DSP Consultants' expertise. Your active projects with major developers in UAE and KSA speak volumes.
Khalid A. Hamidadin
We, Hamdan Studio, express our sincere gratitude to the DSP Consultants team for their exceptional professionalism and unwavering commitment in delivering EL V Design services promptly and with utmost proficiency.
Mohideen Abdul Khader
National Engineering Bureau would like to thank DSP Consultants team for their professional work and commitment to deliver their ELV Design services on time and in professional way. We wish you all the best and looking forward to have long term professional relationship with you.
Sayed Abouelella
Appreciated all the efforts been contributed by your Team and especially by you Asif , and big gratitude for Eng. Fayaz who never leave us alone since the first step of the project till we got the approval, Thank you so much gentlemen and we shall continue the same support.
Our Blogs
Read Story And News
What We do
Explore how we help you
FAQ
Frequently Asked Questions
Q1. Why do businesses need security consultants?
Businesses need security consultants to help them navigate the increasingly complex and evolving threat landscape. Security consultants bring specialized knowledge and expertise to help businesses identify and mitigate potential security risks, which can help prevent losses and protect the organization’s reputation.
Q2. How do security consultants work with businesses?
Security consultants work with businesses in a variety of ways, including conducting security assessments, developing security plans and policies, implementing security measures, and providing training and education to employees.
Q3. How can I choose the right security consultant for my business?
When choosing a security consultant, it’s important to look for someone with the right experience and expertise to meet your specific needs. You should also consider factors such as their reputation, references, and pricing to ensure that you’re getting the best value for your investment. In Abu Dhabi, you can check with one of the top security consultants who is DSP Consultants for more details.
Q4. How much do security consultants cost?
The cost of hiring a security consultant can vary widely depending on the scope of the project and the consultant’s experience and expertise. Some consultants charge an hourly rate, while others may offer project-based pricing. It’s important to discuss pricing and expectations upfront to ensure that both parties are on the same page. Contact DSP Consultants to get a better pricing idea for Security Consultancy Services in Abu Dhabi, UAE.
Contact us