Enterprise Risk Management Consultancy
Enterprise Risk Management (ERM) Advisory Services
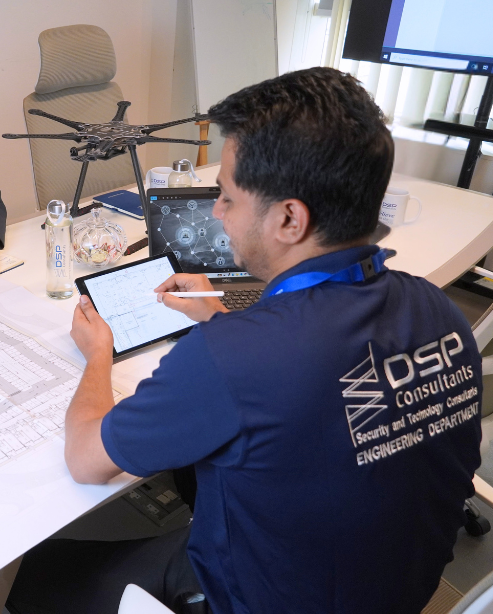
DSP Consultants’ enterprise risk management services provide a structured framework for evaluating risks across the entire organization. We integrate ERM principles into our multidisciplinary expertise to deliver risk-informed design and advisory services.
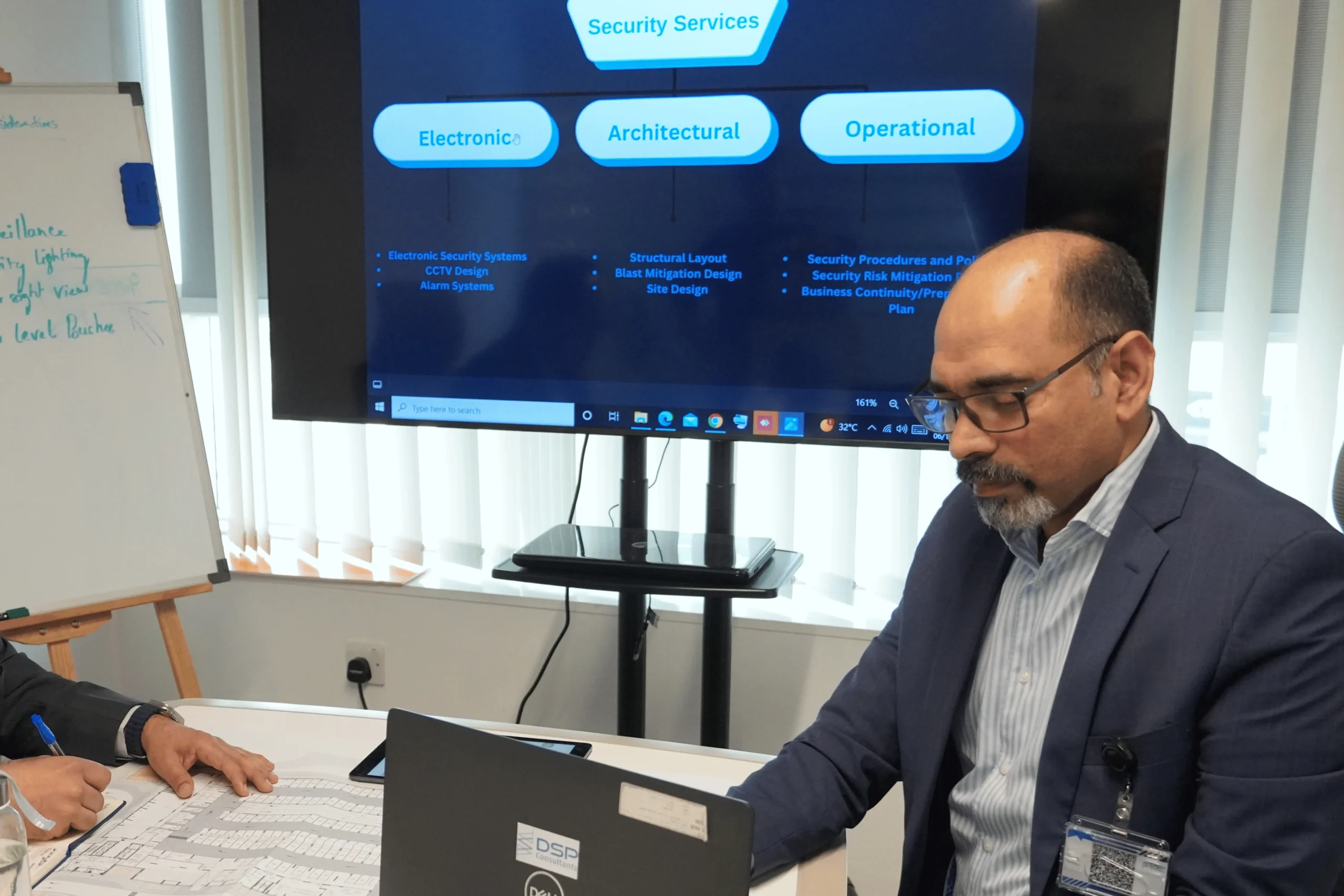
DSP Consultants provide ERM consultancy services aligned with their security master planning services, where they conduct security risk assessments to understand an organization’s vulnerabilities and threats, following which they create a detailed plan that includes all aspects of security design, leading to optimized security risk management.
What is Enterprise Risk Management (ERM)?
Enterprise risk management (ERM) is a comprehensive approach that enables organizations to identify, assess, prioritize, and respond to risks proactively, ensuring the achievement of critical objectives, strategic initiatives, and day-to-day operations.
Without this, businesses risk delayed responses to emerging threats, unmet stakeholder expectations, and increased scrutiny.
ERM helps organizations:
- Avoid unexpected disruptions through early risk identification
- Make informed decisions based on a clear understanding of risk exposure
- Allocate resources efficiently to maximise value
- Align operational activities with strategic objectives
- Ultimately, ERM strengthens resilience and supports sustainable growth.
Our Approach to ERM
DSP Consultants’ experts bring their expertise of security advisory to create a design-led and risk-based approach to ERM, bridging the gap between strategic risk frameworks and practical implementation within the built environment.
Our ERM Focused Services
1. Risk-Based Design Integration
We embed ERM principles into every stage of design by identifying and mitigating risks across disciplines:
- Acoustic Risks: Noise non-compliance, poor occupant comfort, performance failures.
- Security Risks: Threat exposure, vulnerabilities, asset protection gaps.
- ELV Risks: System failures, integration issues, operational inefficiencies.
- Hospitality Technology Risks: Guest experience disruptions, system reliability concerns.
This ensures that every design decision is aligned with risk mitigation and long-term performance.

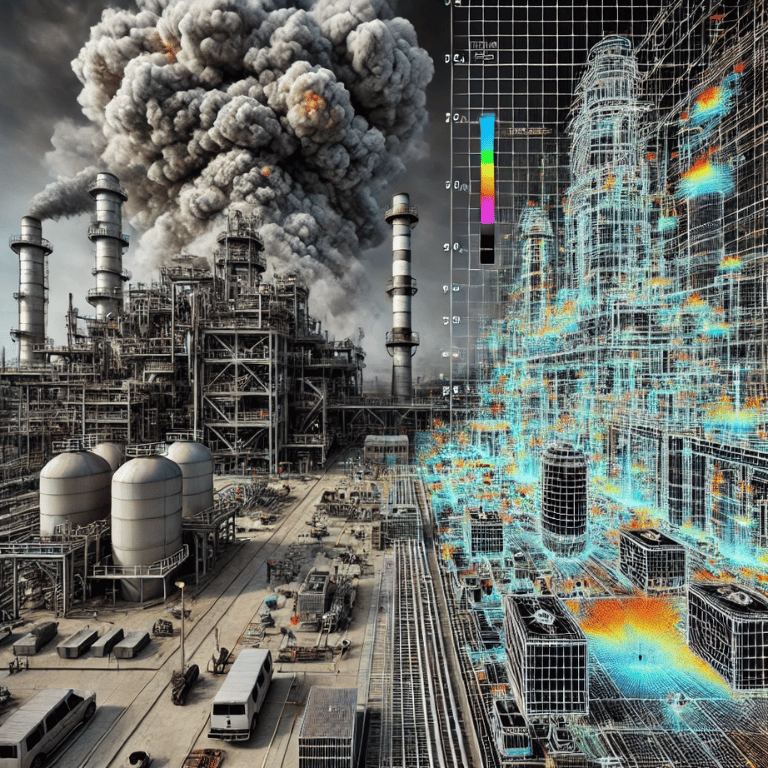
2. Enterprise-Level Risk Assessments
We deliver comprehensive, cross-disciplinary risk assessments tailored for:
- Large-scale developments.
- Mixed-use and hospitality projects.
- Critical infrastructure and high-value assets.
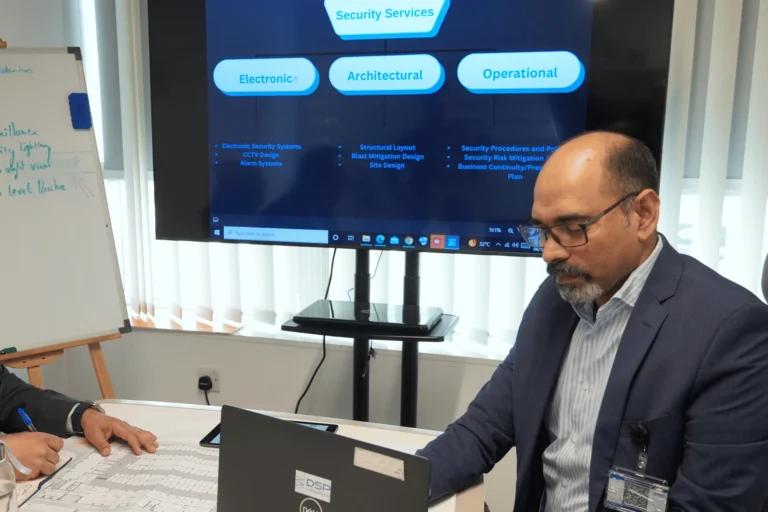
3. Integrated Security & Risk Advisory
Building on our expertise in physical security consultancy, we extend risk assessments to align with enterprise-wide objectives:
- Linking physical security risks to business continuity.
- Evaluating financial, operational, and reputational impacts.
- Supporting compliance with international standards such as ISO frameworks (ISO 31000).
4. Lifecycle Risk Management
Our ERM approach spans the entire project lifecycle:
- Pre-Design: Risk identification and feasibility analysis.
- Design Phase: Risk-informed engineering and system integration.
- Construction Phase: Risk monitoring and compliance validation.
- Operational Phase: Performance audits and continuous risk evaluation
This ensures long-term resilience, not just short-term compliance.
Testimonials
What Our Clients think about Us?

Nithin Mane
Niyo MEP Consultants would like to thank DSP Consultants team for their professional ELV design support services for the hospitalitality projects. The quality of the design was outstanding and the scope of work was delivered on time. We will be happy to work with you again in the future.
Zaid Rababa
I am Impressed by DSP Consultants' expertise. Your active projects with major developers in UAE and KSA speak volumes.
Khalid A. Hamidadin
We, Hamdan Studio, express our sincere gratitude to the DSP Consultants team for their exceptional professionalism and unwavering commitment in delivering EL V Design services promptly and with utmost proficiency.
Mohideen Abdul Khader
National Engineering Bureau would like to thank DSP Consultants team for their professional work and commitment to deliver their ELV Design services on time and in professional way. We wish you all the best and looking forward to have long term professional relationship with you.
Sayed Abouelella
Appreciated all the efforts been contributed by your Team and especially by you Asif , and big gratitude for Eng. Fayaz who never leave us alone since the first step of the project till we got the approval, Thank you so much gentlemen and we shall continue the same support.
other services
Explore how we help you
Explore our array of top-notch design, consulting, and engineering solutions tailored for the Middle East and Africa region.
Our Blogs
Read Story And News
Discover our blog, where we share valuable insights, industry trends, and expert tips on ELV and security design, keeping you informed and inspired in the ever-evolving world of technology and security.
FAQ
Frequently Asked Questions
Q1. Wonder what comes after security threat and risk assessment?
It is a security master plan that is created as a detailed master plan document, which is a comprehensive guide outlining security strategies, goals, and procedures, including reports, drawings, and illustrations.
Q2. Now wondering what the purpose of this security master plan document is?
It is to take a collaborative approach at the initial stages of a project by landscape architects, civil engineers, or developers, to then come to a decision with stakeholders on how to mitigate security risks.
Q3. What are the benefits of security master planning?
- Cost-efficient – saving modifications during the design process
- Revealing Vulnerabilities – clear knowledge of your threats helps you be prepared for them in the future to continue work even in times of uncertainties
- Creating a safe environment – After planning and mitigating risks you provide a safer environment for everyone fostering the use of that specific environment.
Contact us
COMPANY CERTIFICATIONS